Which Type to Use and When
You get a ticket: “Give the data team read access to one folder in S3.” Simple…until you have to decide how. You’ve had S3 IAM policies on your to-do list for months. Do you:
- Update the bucket policy?
- Attach an IAM policy to a role?
- Use a permission set in IAM Identity Center?
- Try S3 Access Grants because you’ve heard it’s “the future”?
All of these can solve the problem. Only one is the right long-term choice.
For AWS administrators, especially in growing environments, the real challenge is making sure it still makes sense six months later, when your environment has doubled and someone asks, “Who has access to this data?” The good news is that you don’t need a full-blown security overhaul. Most organizations can get visibility and control back in a single afternoon using native AWS tools.
Why S3 Permissions Get Complicated
Rather than designing their IAM model upfront, most teams evolve it under pressure.
- A new app needs access? Add an IAM role.
- A partner needs cross-account access? Add a bucket policy.
- Security raises a concern? Add an SCP.
- Someone mentions a best practice? Add…something else.
Individually, each decision is reasonable. Over time, they create a layered system without a clear structure. That’s when you start seeing:
- Duplicate permissions across policy types
- Overly broad access “just to make it work”
- Long debugging cycles when access breaks
- Audit findings that are technically correct—but painful to fix
The issue is that most teams are missing a consistent decision framework (it’s not AWS’s fault).
A Layered Model That Scales
Instead of choosing policy types based on habit, anchor each decision to a specific layer. Each layer has one job.
1. Organization Layer: What is allowed at all?
This is your baseline security posture.
- Service Control Policies (SCPs) restrict what accounts and principals can do.
- Resource Control Policies (RCPs) restrict how resources can be configured.
Use this layer to enforce non-negotiables:
- No public S3 buckets
- Encryption required
- TLS-only access
These policies define the boundaries. If your organization is growing, this layer becomes critical for maintaining consistency without constant oversight.
2. Identity Layer: Who or what is acting?
This layer defines your principals.
- IAM identity-based policies attach to roles and users.
- Permission boundaries limit what delegated roles can do.
Use this for:
- Application and service access (EC2, Lambda, ECS)
- Internal platform roles
- Controlled delegation to teams creating their own roles
If it’s a workload or system component, this is almost always the right place.
3. Resource Layer: What does the bucket allow?
This is where bucket policies belong. They define how the S3 resource itself can be accessed, regardless of identity configuration. Use bucket policies for:
- Cross-account access
- Network-based restrictions (VPC endpoints, IP ranges)
- Enforcing conditions like aws:SecureTransport
A useful test: if you deleted all IAM policies, would this rule still make sense? If yes, it likely belongs in the bucket policy.
4. Access Layer: Who gets access to which data?
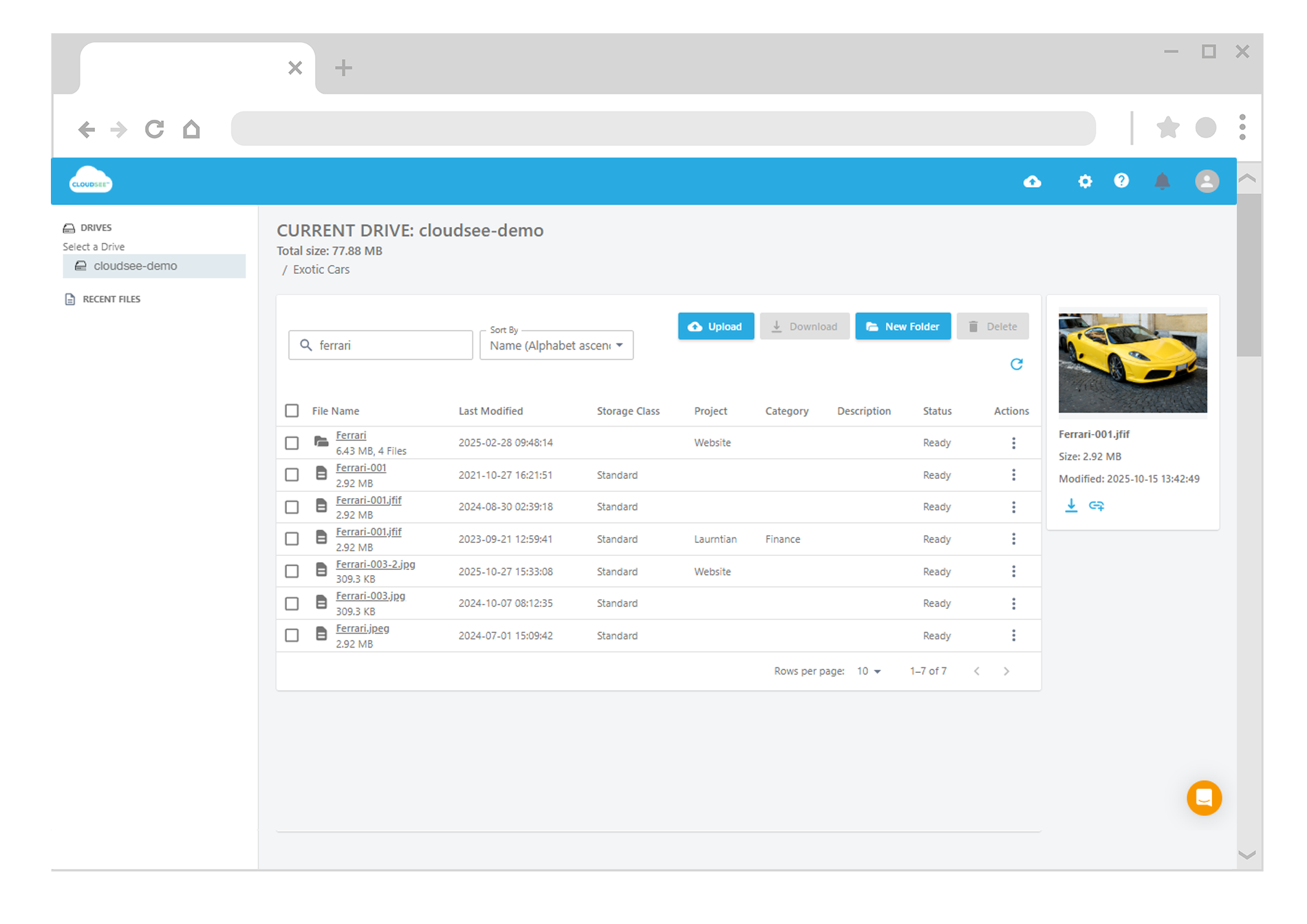
Many teams still rely too heavily on bucket policies and where things break down at scale. S3 Access Grants (with IAM Identity Center) are purpose-built for this layer:
- Map users and groups directly to S3 prefixes
- Avoid complex, hard-to-maintain bucket policies
- Provide cleaner audit visibility
For example, instead of embedding user access rules into a bucket policy, assign your finance team access to:
s3://company-data/finance/
No JSON editing. No unintended side effects.
For growing teams, this is one of the highest leverage changes you can make.
5. Session Layer: Is the access temporary?
Not all access should be persistent.
- Session policies apply during AssumeRole operations
- They scope down permissions for a specific session
Use this for:
- Temporary elevated access
- Just-in-time workflows
- Limiting risk during sensitive operations
It’s a simple way to reduce blast radius without redesigning your entire IAM model.
Why IAM Policies Matter for AWS Admins
If you’re responsible for uptime, security, and scalability. This is not just theoretical. A clean policy model directly impacts:
Operational speed
Access requests become predictable and faster to fulfill, especially when using Access Grants instead of manual policy edits.
Security posture
Clear separation of concerns reduces over-permissioning and makes misconfigurations easier to detect.
Audit readiness
When each layer has a defined role, audits shift from “investigation” to “verification.” In other words, fewer surprises and fewer fire drills.
Where to Start (Without Breaking Everything)
You don’t need a full redesign to see improvement. Start with one recent request:
- Identify which layer it belongs to
- Move it to the appropriate mechanism
Common quick wins:
- Replace human access in bucket policies with Access Grants
- Move org-wide rules into SCPs or RCPs
- Tighten overly broad IAM policies for service roles
You’re building a system that stays understandable as your AWS environment grows. You can iterate as you learn. The end goal is secure and explainable access.


Leave A Comment