How to Enforce Tags Before the Bill Arrives
Once again, your Amazon S3 bill jumped. You spark up Cost Explorer, filter by service, and hit a wall. Dozens of buckets have no cost center, no owner, no environment tag. Just a creation date and a mounting total. Untagged S3 buckets are quietly expensive. S3 storage itself is not overpriced; without tags, you lose visibility to connect usage to teams, projects, or business outcomes. Untagged objects turn your AWS bill into a black box.
Why “Untagging” Keeps Happening
The real problem is structural friction. AWS doesn’t require tags when creating a bucket. Developers on a tight deadline spin up storage mid-sprint, thinking they’ll “tag later.” Unfortunately, “later” rarely comes. Fast forward a few months: multiple teams, hundreds of buckets, no consistent tagging schema. Maybe you have documented a tagging policy…but there’s no enforcement. When templates skip the tags block in Terraform or CloudFormation, chaos builds invisibly.
Tagging slips through the cracks because AWS allows them to, not because people forget.
The High Cost of Inaction
Every untagged bucket compounds confusion and waste. Without AWS Cost Allocation Tags, you can’t break down spend by project or team. Untagged resources land in an unhelpful “No Tag” bucket that ruins chargeback visibility and forecasting.
Flexera’s *State of the Cloud* report consistently shows that roughly a third of cloud spend is wasted. Lack of resource visibility is one of the primary reasons. Security suffers too. Untagged buckets are unclassifiable, making it difficult to automate data sensitivity policies, enforce lifecycle management, or properly audit. Operational pain follows: incident response slows to a crawl when every engineer starts with, “Wait, whose bucket is this?”
How to Enforce Tagging Before Buckets Are Created
Tag governance works best when automated and preventive. Here’s how to enforce tagging systematically before storage ever spins up.
Service Control Policies (SCPs)
SCPs are the gold standard for AWS Organizations. Create an SCP that denies `s3:CreateBucket` unless required tags are included in the request. No tag, no bucket. Attach this policy to your dev or test organizational units (OUs), and you’ll stop untagged bucket creation at the source.
IAM Condition Keys
For single-account setups, attach IAM policies using `aws:RequestTag` conditions to your provisioning roles. This enforces tags for anyone creating buckets without the need for Organizations.
AWS Config Rules
Detect the buckets that slipped through. The managed rule `required-tags` flags non-compliant resources. When paired with Systems Manager automation, you can auto-remediate by applying fallback tags.
IaC Guardrails
Bake tagging compliance into your pipeline.
- Terraform: Use tflint with a required-tags plugin to scan before `terraform plan` runs.
- CloudFormation: Validate tag policies with CloudFormation Guard (cfn-guard) before stack deployment.
The lesson: tagging shouldn’t depend on memory. It should depend on policy.
CloudSee Drive = Visibility Comes First
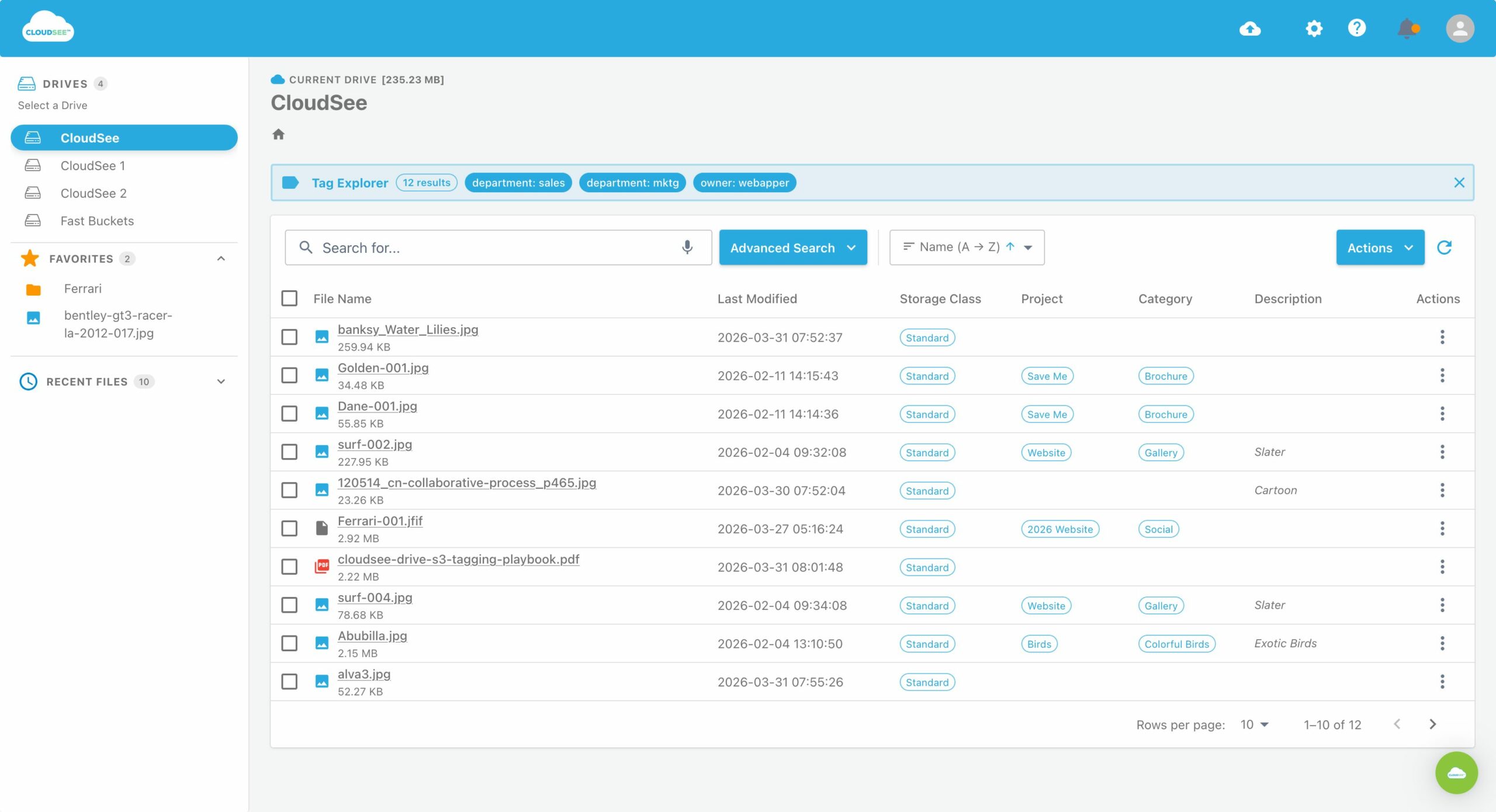
Before enforcing forward, you need to fix backward. CloudSee Drive’s browser-based Tag Explorer displays tag data, helping teams visualize what’s tagged, what’s not, and who owns what. No CLI scripts, no spreadsheets…just simple visibility. Identify untagged objects, and prioritize cleanup efforts without jumping between AWS console screens. It’s the missing link between tagging policy and real enforcement.
Tying It All Together
Your confusing S3 bill was a governance issue, not a budgeting issue. With the right guardrails in place:
- SCPs prevent future messes.
- AWS Config catches missed tags.
- CloudSee Drive closes the visibility gap.
Tag enforcement is the connective tissue between finance and engineering. When every bucket carries a clear owner, cost center, and environment tag, your cloud stops being a mystery. It becomes manageable. Take control before the next billing cycle. CloudSee Drive helps you audit, tag, and govern your S3 storage with full visibility before the bill arrives.

Leave A Comment