One of the areas we looked at in our article about cleaning up after your developer leaves was access. Undocumented access to your Amazon S3 buckets is a challenge that pops up often. It can happen to any AWS admin. Say you’ve got buckets you set up two years ago. Some you remember, and some you don’t (that one named `temp-client-files-2025` you keep meaning to double-check). Three vendors still have access keys you issued during an integration project, and if you’re honest, at least one of those vendors isn’t even working with you anymore. Somewhere in your AWS account, a former contractor probably still has read access to production data. And there’s a good chance one of your buckets is publicly open right now…not from malice, but from a small configuration slip that happened 18 months ago and never got caught. This isn’t fearmongering. It’s reality in public S3 buckets. In 2025, over 20% of cloud data breaches began with an exposed S3 bucket. Not zero-day exploits, just forgotten permissions.
The good news is that you don’t need a full-blown security overhaul. Most organizations can get visibility and control back in a single afternoon using native AWS tools.
Why S3 Access Slips Out of Control
S3 access management is far more than one simple setting. It’s a mix of three overlapping systems that can contradict each other:
IAM policies
Govern who within your AWS account can interact with S3.
Bucket policies
Control access at the bucket level.
Access Control Lists (ACLs)
The older, often-forgotten layer AWS is phasing out but still used in legacy buckets.
Any one of these can open a hole, even when the others look locked down. Typical causes at small and mid-size organizations:
- IAM roles created for integrations that never get cleaned up
- Bucket policies copied from Stack Overflow with `”Principal”: “*”` — meaning *everyone*
- Block Public Access incorrectly assumed to apply across both account and bucket levels
- No centralized inventory of who can access what
These issues are about bandwidth. With one or two overworked admins managing everything, S3 security naturally drifts over time.
Why You Really Should Fix Public S3 Buckets ASAP
Roughly half of all S3 buckets have misconfigurations that expose data to the internet. The average small-business breach tied to S3 mismanagement costs over $1.7 million, before factoring compliance and reputation damage.
Three reasons to take action now:
- Auditors notice. SOC 2, ISO, or vendor security reviews all include S3 access checks. “We’re not sure who has access” won’t fly.
- Legal inquiries won’t wait. You don’t want to scramble if someone requests proof of who accessed `temp-client-files-2022`.
- Access keys never expire. Vendor credentials, once issued, keep working until you explicitly revoke them.
How to Audit S3 Bucket Access Control
Everything you need exists already within AWS. Here’s how to get clarity today:
1. Enable IAM Access Analyzer.
Instantly flags publicly accessible buckets or cross-account sharing. IAM Access Analyzer is free, continuous, and takes minutes to enable.
2. Check Block Public Access (account and bucket level).
Account-level settings act as a global fail-safe, but individual buckets can override them. Verify both.
3. Review bucket policies for `”Principal”: “*”` entries.
If you see it and can’t explain why, remove it. That’s the most common accidental exposure.
4. Audit IAM users and roles with S3 permissions.
Sort by last-activity date. Anything dormant for 90+ days may no longer need access. Pay attention to hardcoded credentials in integrations.
5. Inspect Lambda and EC2 roles.
Many functions have overbroad S3 permissions like `s3:*` on `*`. Tighten these to the specific resources needed.
6. Automate quarterly reviews.
Treat public S3 bucket access management as routine hygiene…like patching servers or rotating passwords.
The Real Threat Is Automation, Not Hackers
The exposure you’ll face first likely won’t be a targeted attack. It’ll be an automated scanner combing AWS for open buckets, grabbing data before you’ve finished your morning coffee. Locking down access doesn’t require new tools…just consistent attention.
TL;DR
Too many AWS admins lose track of who can access their S3 buckets.
Misconfigurations pile up…IAM drift, old vendor keys, public policies. And before long, sensitive data is exposed.
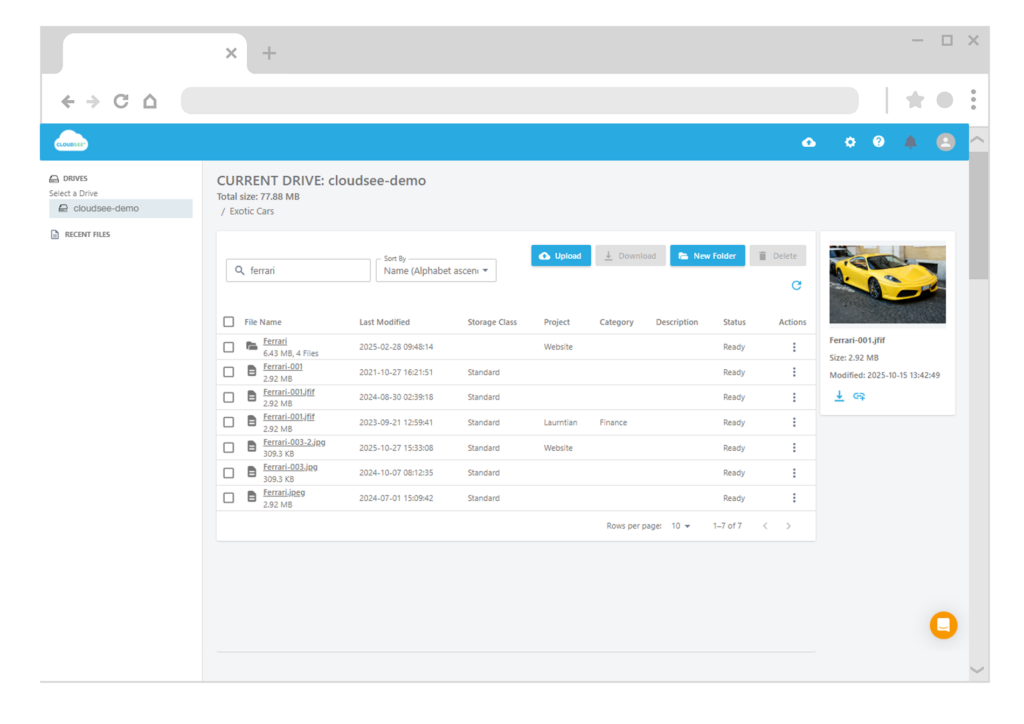
Use native AWS tools like Access Analyzer and consistent access reviews to stay secure. CloudSee Drive adds visibility across all your S3 buckets in one place.


Leave A Comment